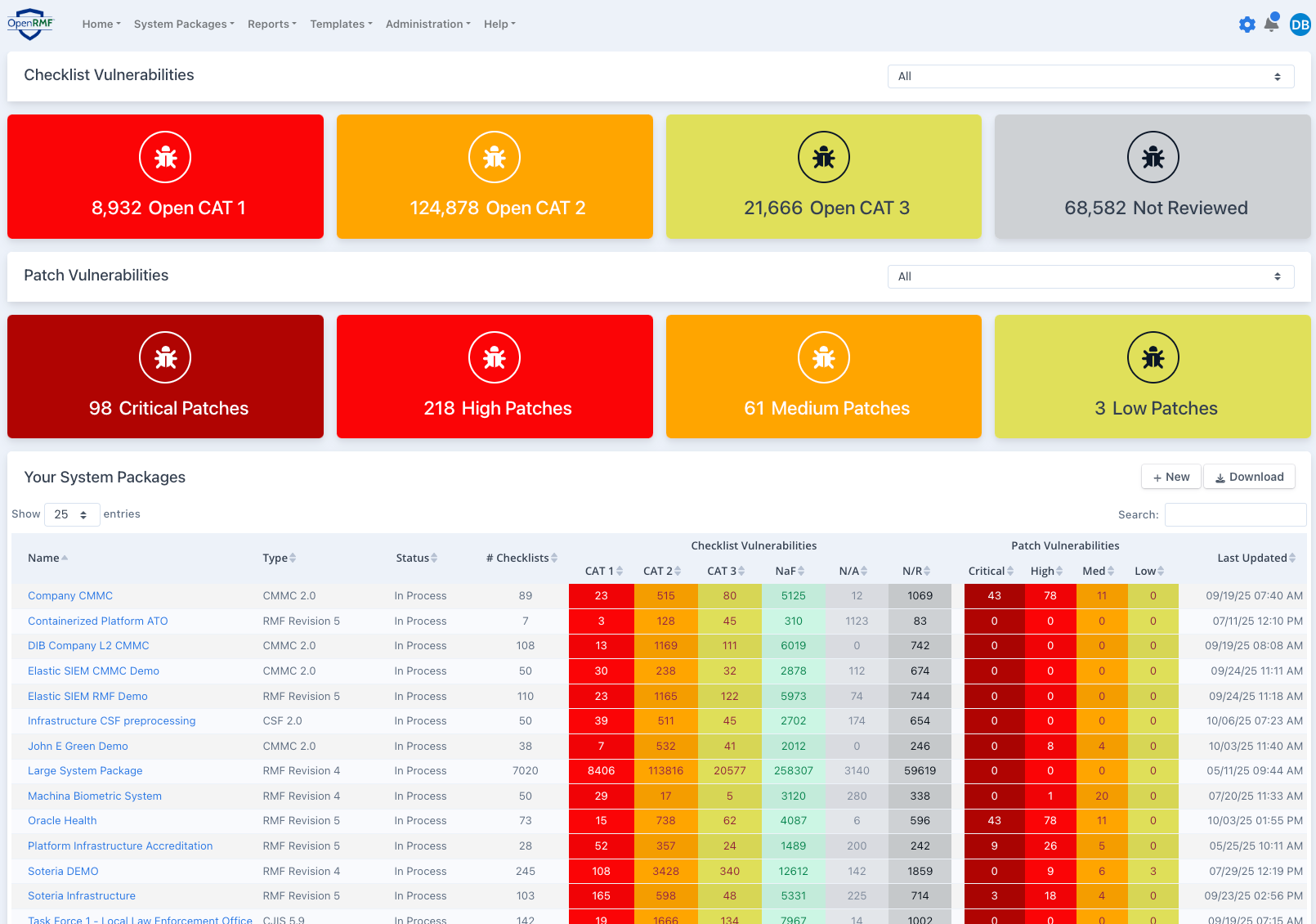
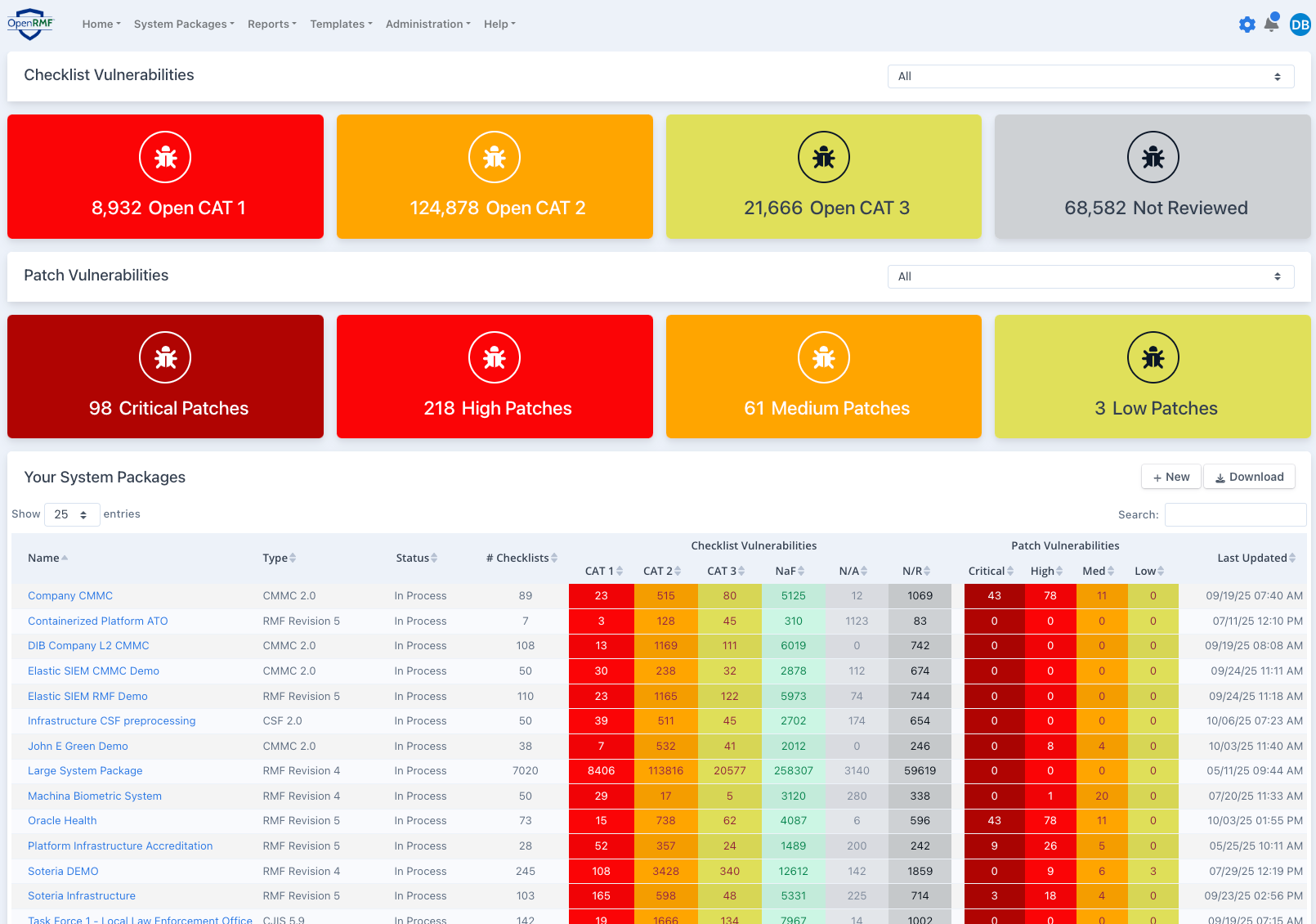
View all ATOs and accreditation packages across your entire portfolio in seconds
See active compliance status, open vulnerabilities, POAM and trends easily
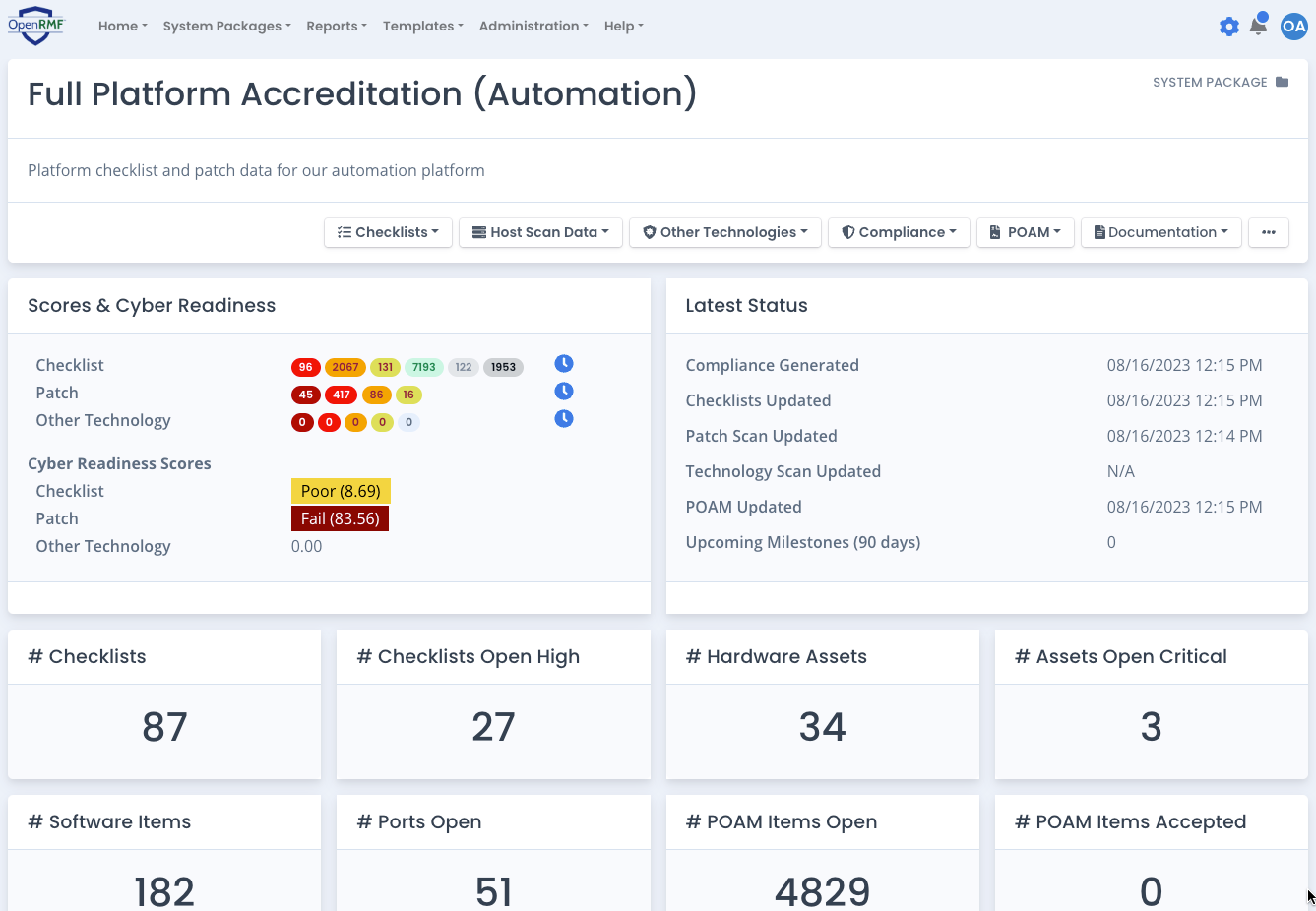
Quickly see compliance status, open items, status, risk, and continuous monitoring activity
Gain insight into your ATO's, vulnerabilities and POAM updates directly in seconds
Upload scans, track open items, watch trends, and report on your devices quickly
Get POAM status updates, vulnerablity updates via notifications, and run reports
Automate and Track all STIG Checklists, Patch Vulnerabilities, Software and Hardware, PPSM, Tailoring, Overlays, CCRI, reporting and more from a single web-based application. Built in history, configuration management, and trends show you where you were, where you are, and where you need to go.
Use Team Subpackages to limit access to areas of your entire accreditation package. Export out your artifacts for uploading into your program of record.
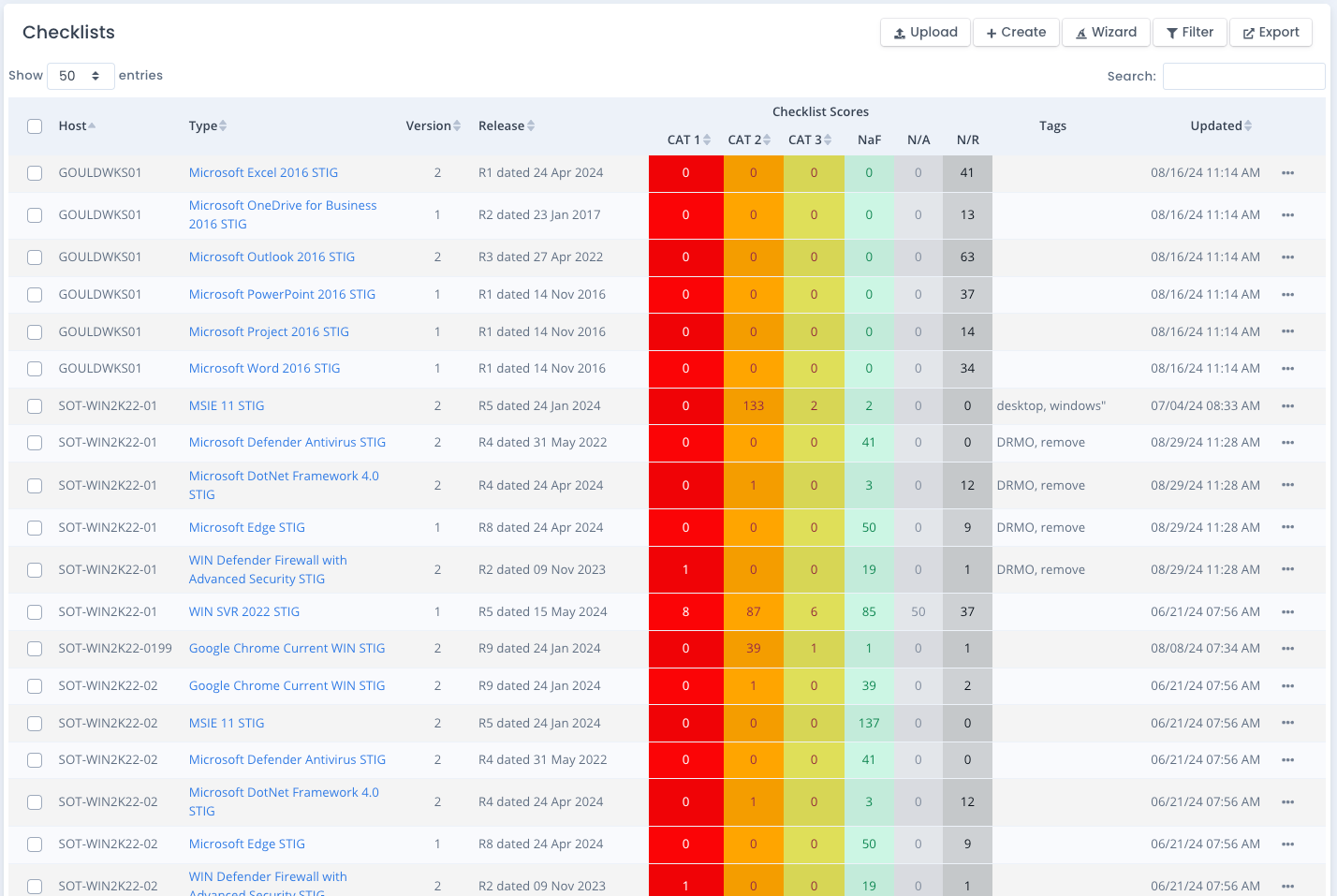
OpenRMF® Professional gives you a single definitive source-of-truth for all DISA, CIS, and Custom Checklists across your entire system package.
We read in raw SCAP scan results, CKL/CKLB checklist files, Nessus Audit Compliance Scans, and Tanium CSV SCAP results. And then track your checklists from there. You can even create CIS benchmark checklists.
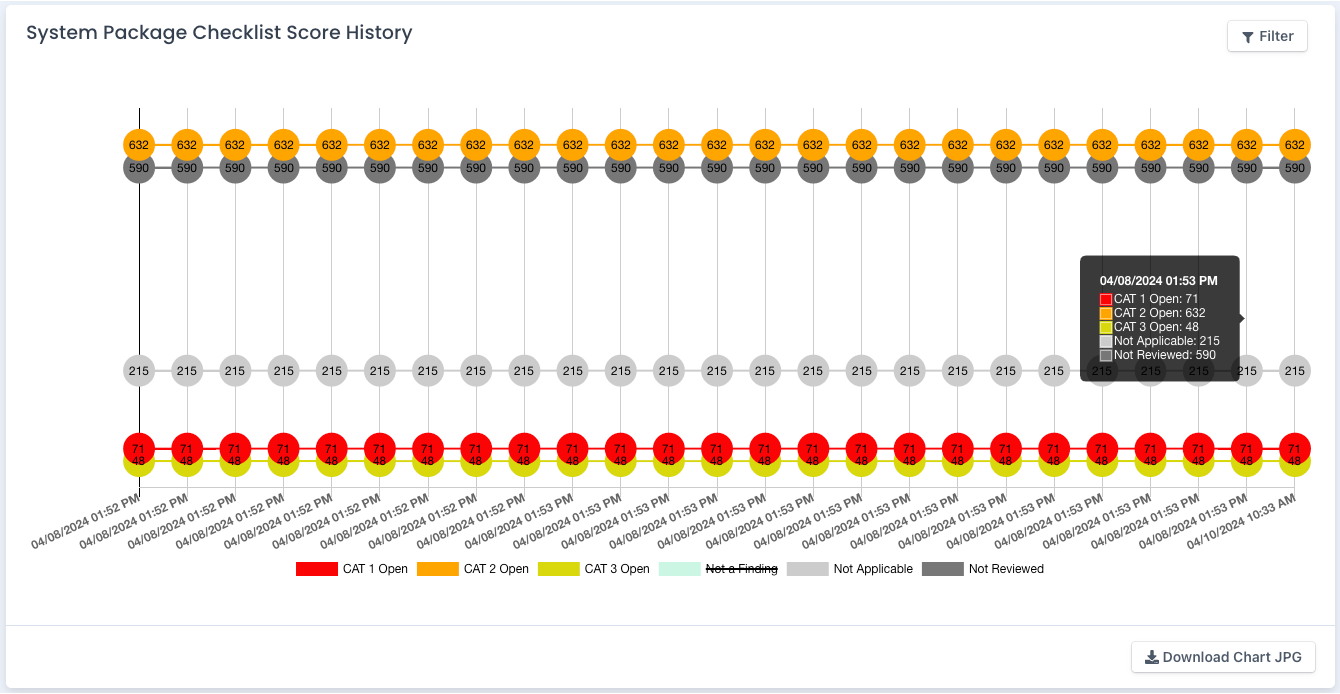
Track your vulnerability counts automatically at all levels. And bulk lock, bulk edit, and generate compliance with a couple clicks. Use the Checklist Applicability Wizard to add required checklists as well.
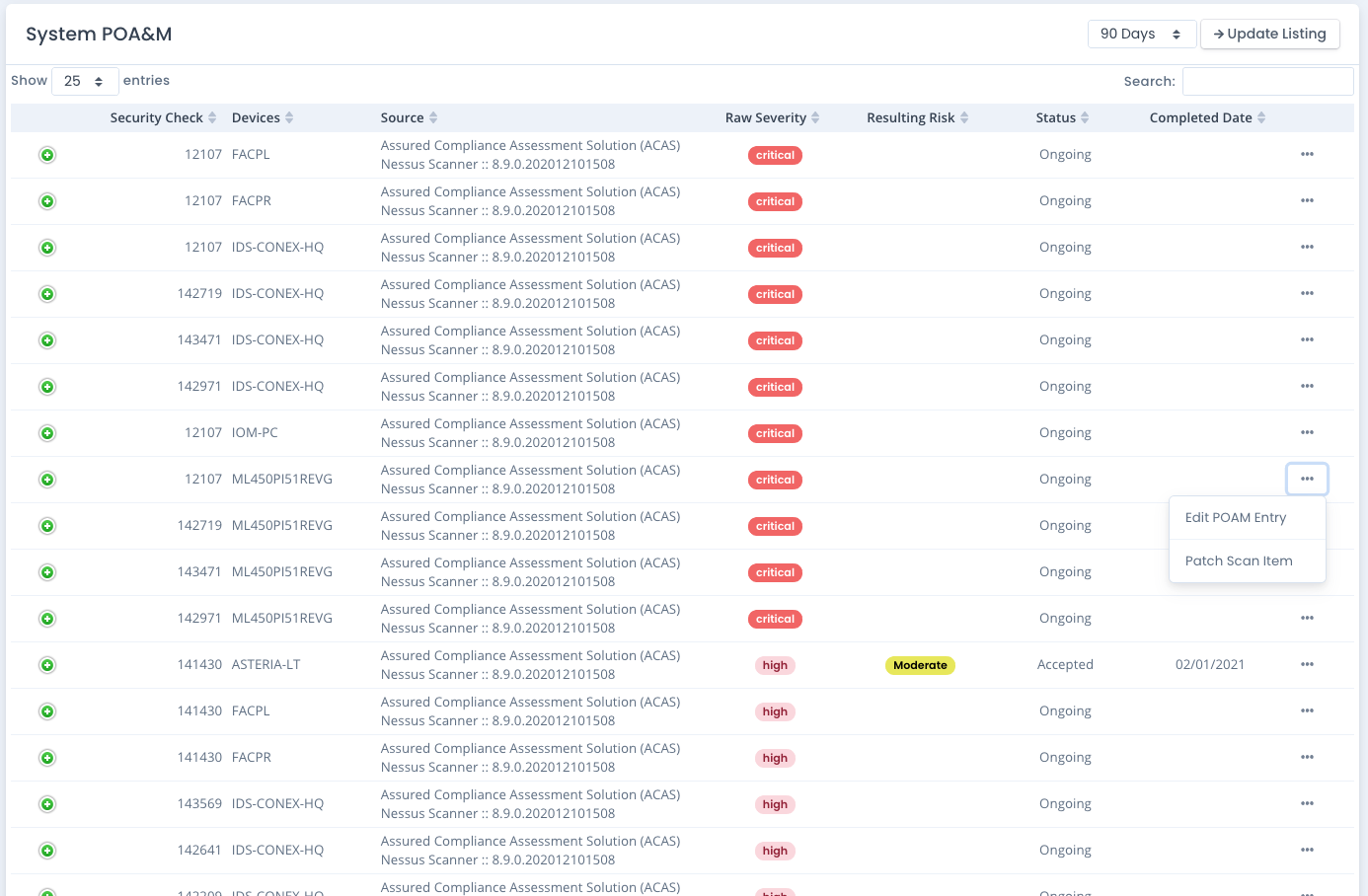
Remove the manual, cumbersome, error-prone editing of your POAM status on vulnerabilities and open items. Let OpenRMF® Professional automate that work for you!
With bi-directional traceability, you can add and update entries automatically based on your latest scans, edits, compliance statements and inherited controls. Export to a proper POAM XLSX file for your program of record.
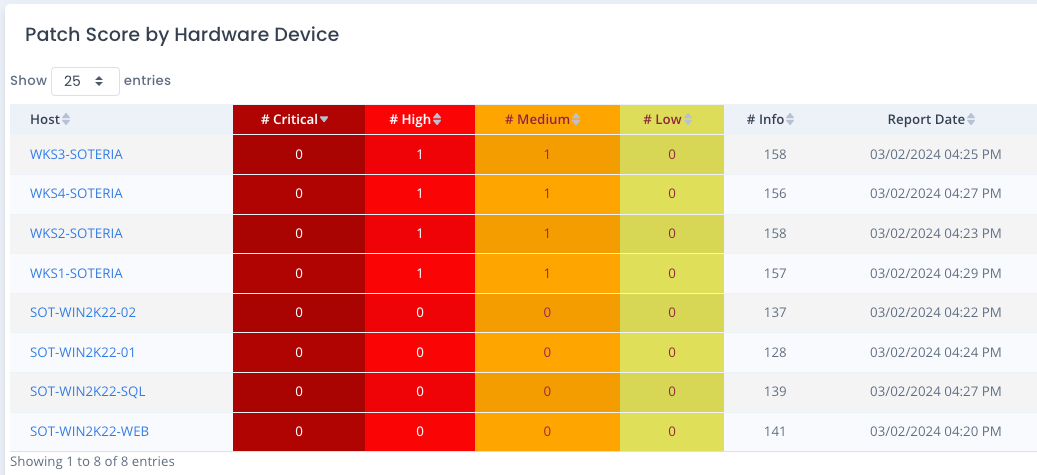
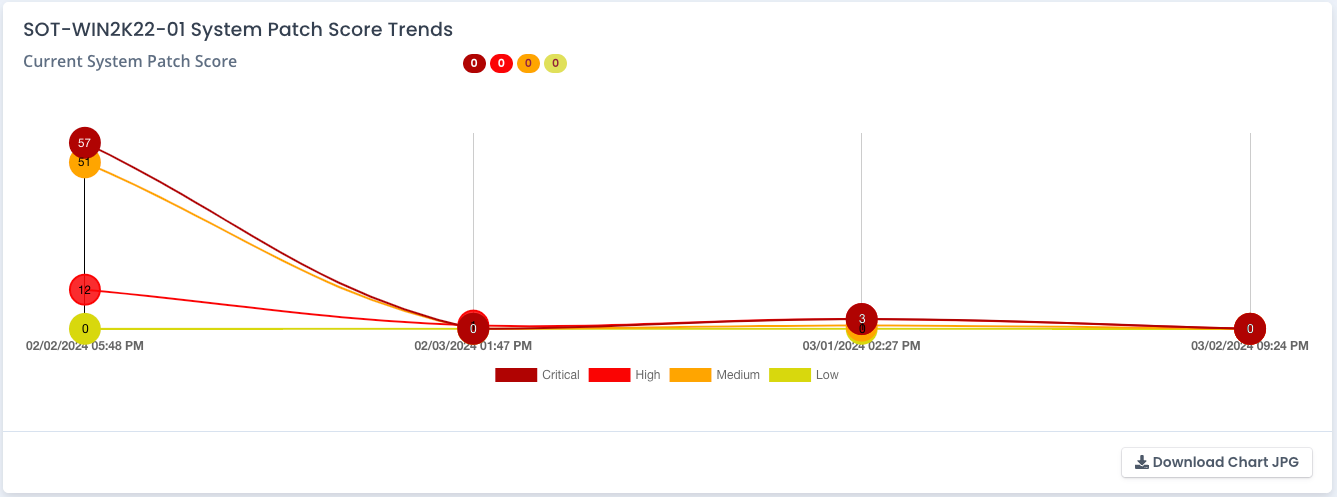
Upload your Tenable Nessus, Rapid7 Nexpose or custom patch vulnerability results easily. Track your trends, open vulnerabilities, and devices for updates and compliance over time.
Export chart JPG or Excel listings for reporting, tasking, submission. Automate for continuous monitoring made easy!
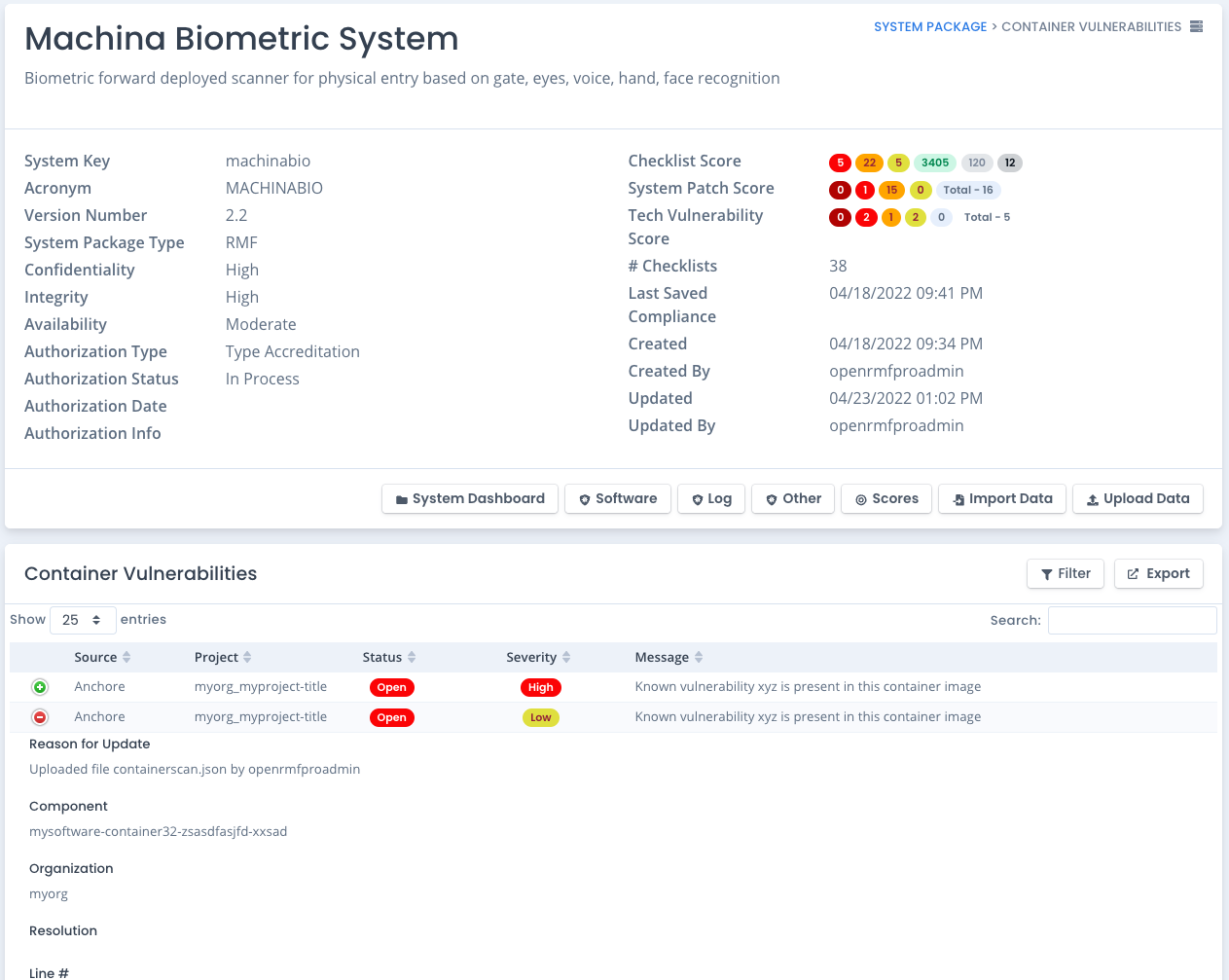
Import or Upload other vulnerability data from software scans, container scans, log scans, infrastructure as code scans, or other types of scans to view other vulnerabilities as well. Track trends of vulnerability data for other areas just like compliance and patches.
Export chart JPG or Excel listings for reporting, tasking, submission. Automate for continuous monitoring made easy!
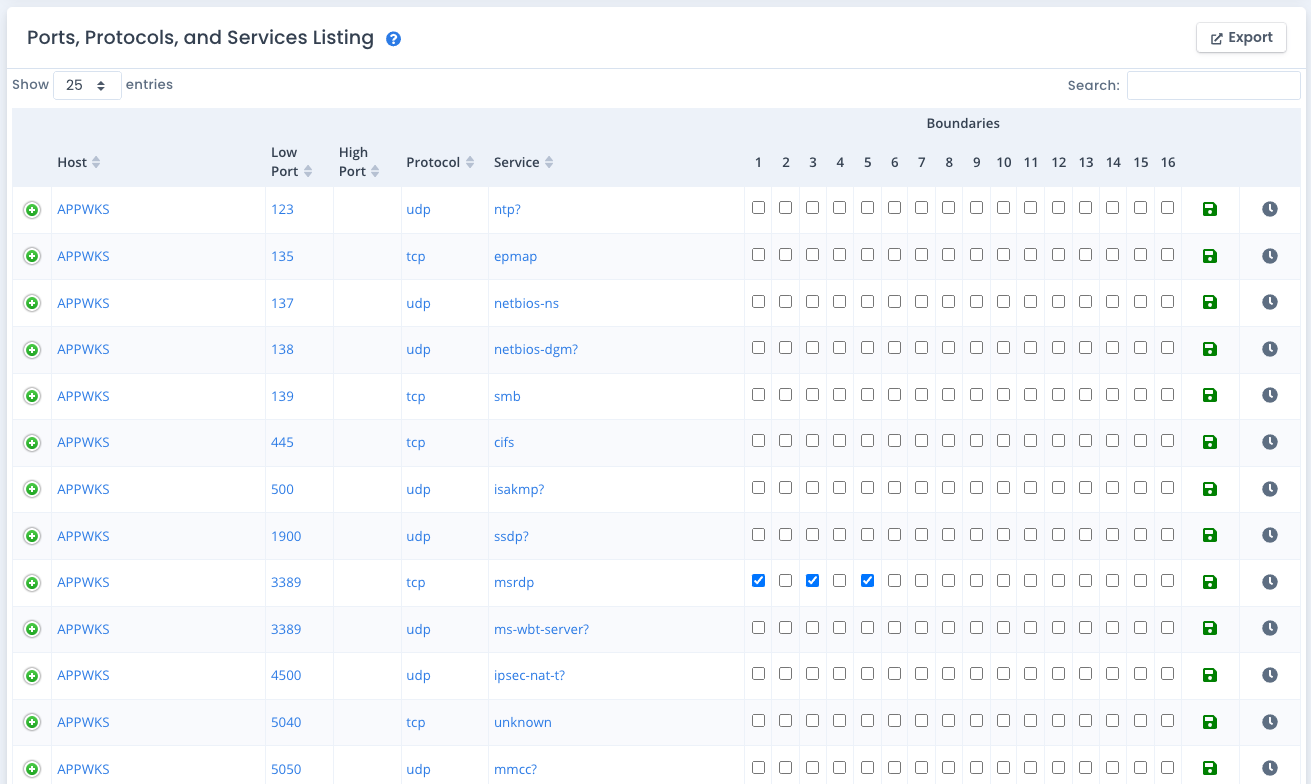
Automatically pull PPS data from your patch vulnerability scans across all devices. Upload additional listings for those items that cannot be scanned. Easily enhance this data by specifying any boundaries they cross for reporting, tracking, data calls, and identifying your security posture.
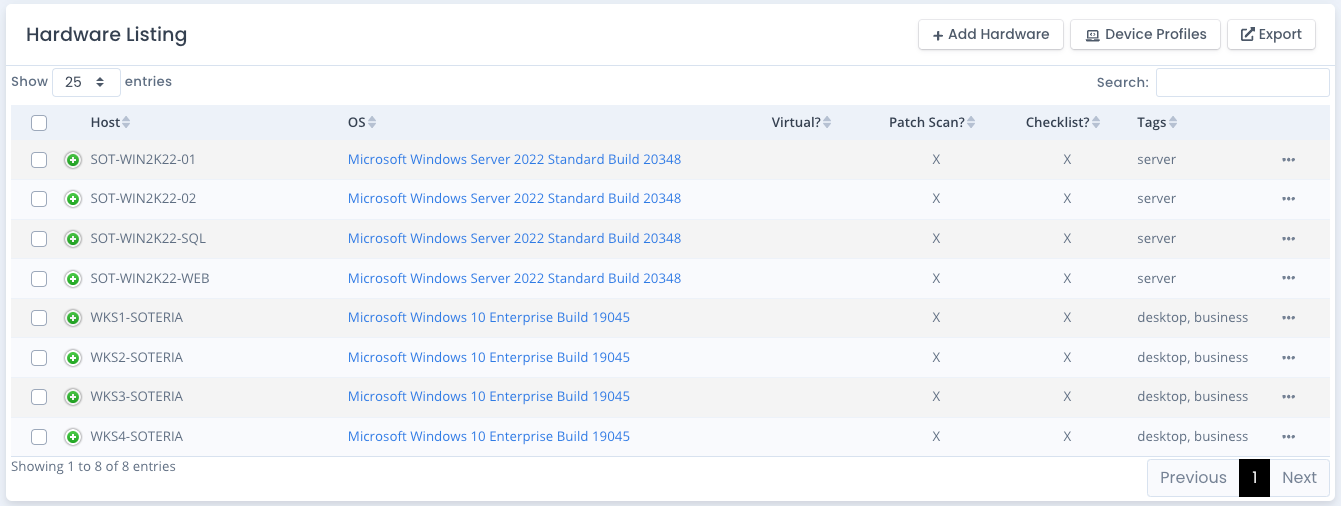
Automatically track hardware devices from compliance scans and patch scans. Upload additional devices and data to enhance this listing from other asset management sources.
Automatically pull software listings from your patch scans as well. And you can Upload additional devices and data to enhance this listing from other sources as well.
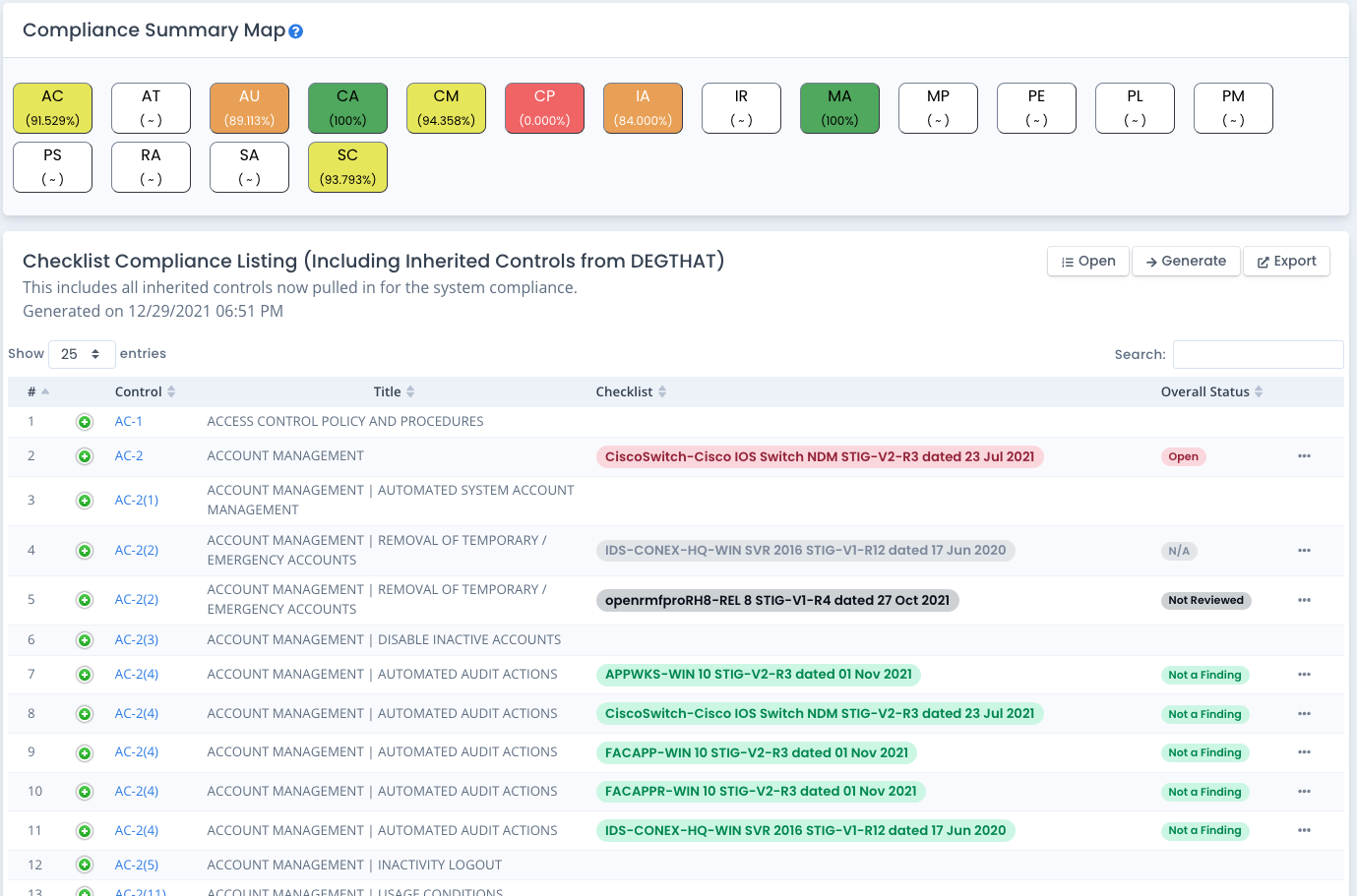
OpenRMF® Professional allows you to generate compliance based on all your DISA, CIS, and Custom Checklists against your compliance and compliance levels. Whether RMF, FedRAMP, CMMC, CSF, ISO, IEC, or a custom framework you build and load.
You can tailor controls in and out. And add overlays on top of that list of controls to see a true compliance listing in seconds. Dive into checklists and compliance statements filtered by your control listing.
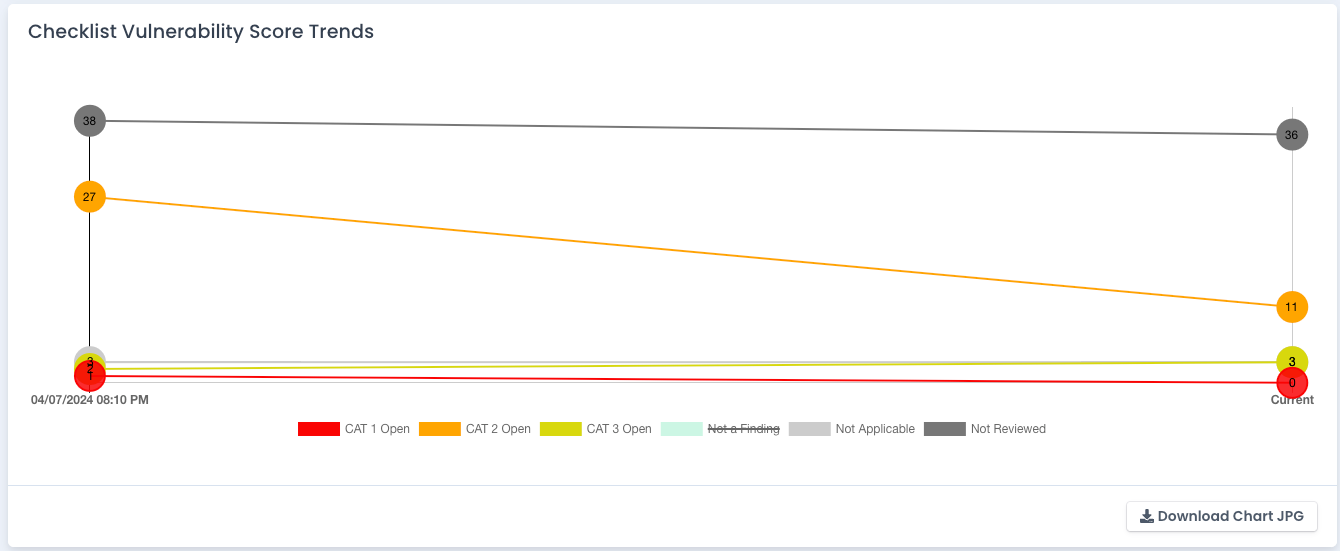
See historical charts of your entire system package compliance, checklists, and vulnerability numbers over time. See trends of compliance percentage by NIST control family or subcontrol as well.
Export charts to JPG for use in reports and updates. Automate for continuous monitoring made easy!
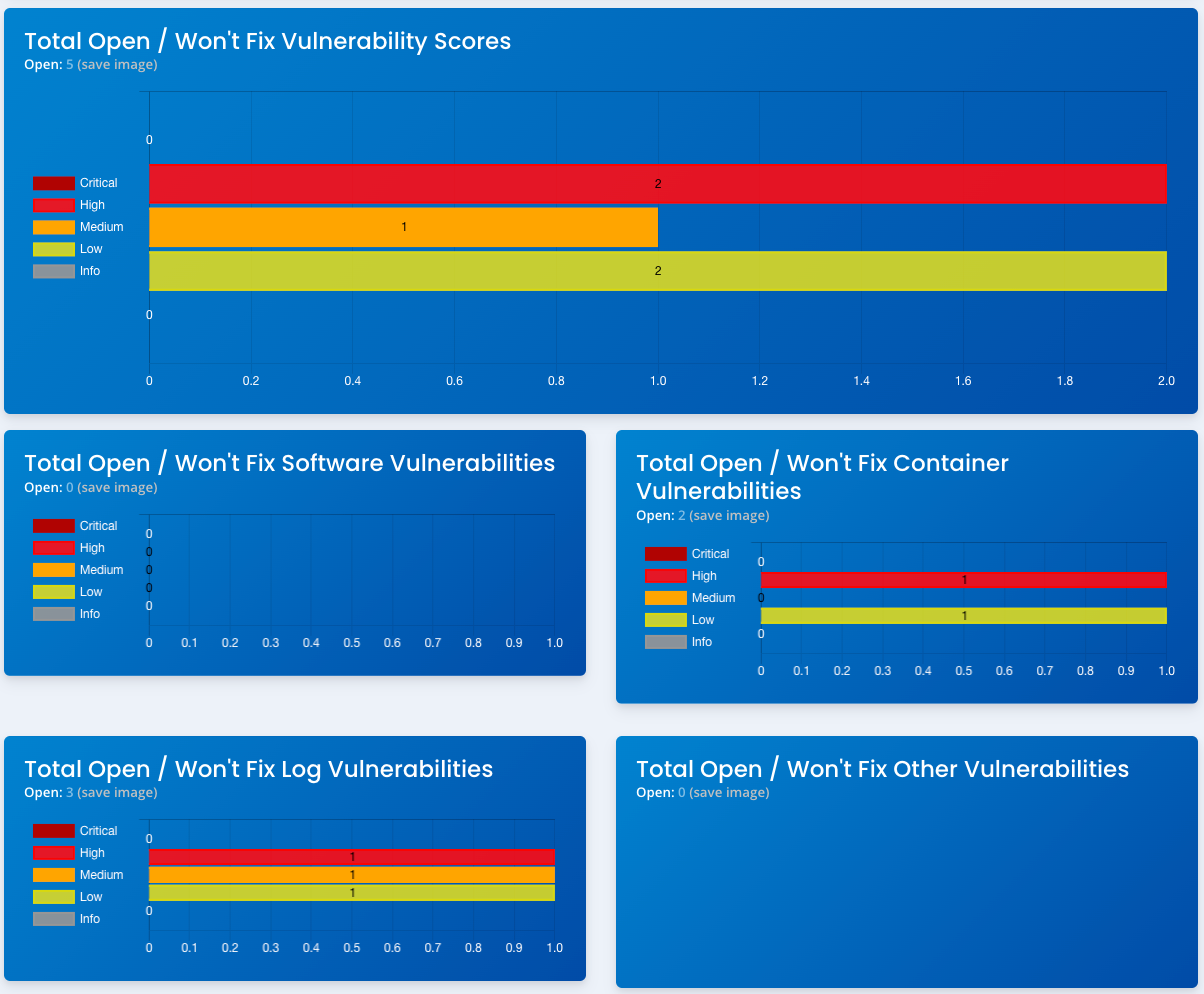
OpenRMF® Professional now includes a way to import, upload, or post (via API) other vulnerability data for your system package. Whether its from Fortify or SonarQube static scans, container scans, or other types of scans you can easily import or upload data to track those vulnerabilities and their score within your larger system package.
Combined with our API you also can plug this into a DevSecOps process or an even larger integration with your Software Factory to incorporate all scans and vulnerability data to allow tracking, gated deployment/delivery and other pipeline features for your automation.
Receive notifications on updated checklists, uploaded patch scans, hardware and software listings, as well as changes in ports, protocols, and services automatically.
Team notifications across the system package are automatically filtered by access to that particular accreditation package or Team Subpackage.

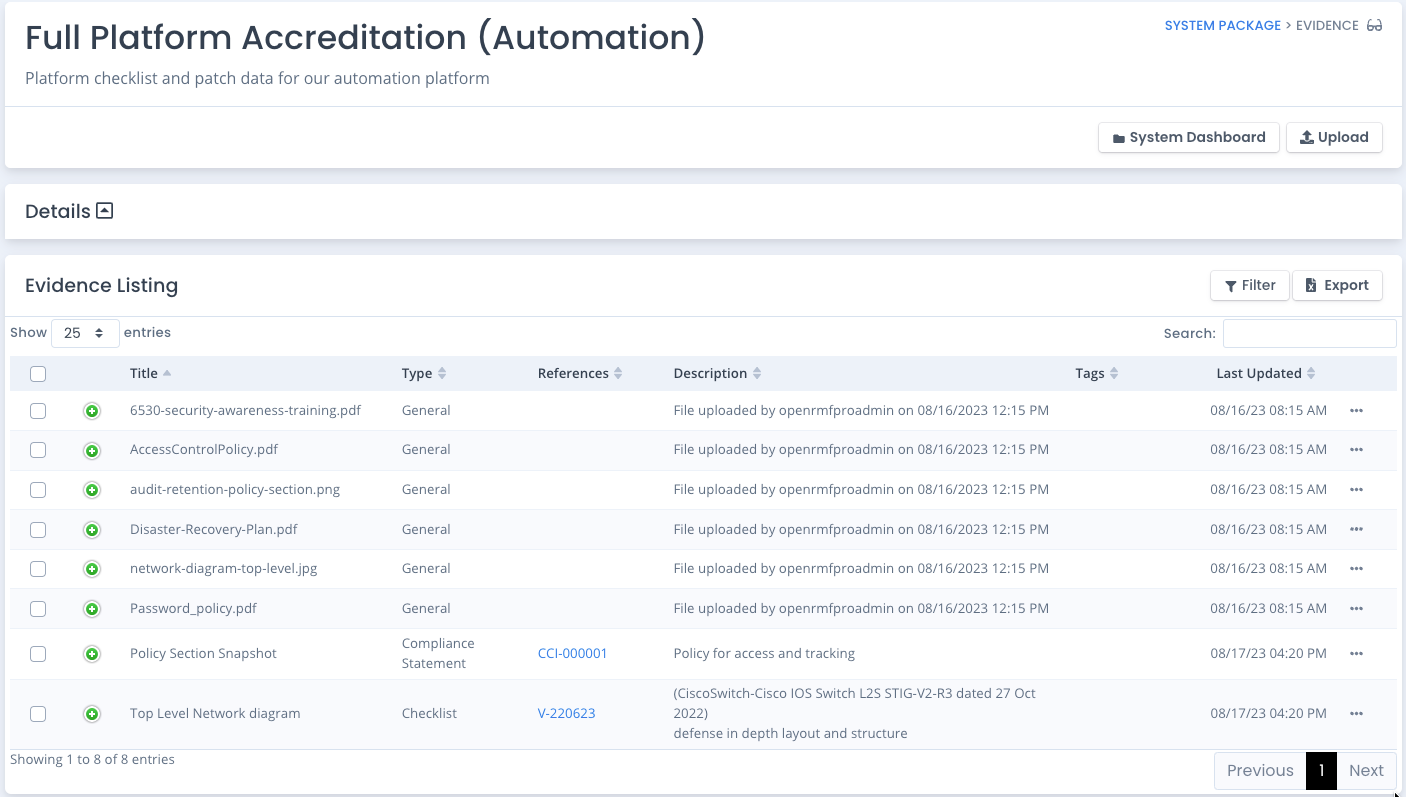
Upload evidence on policy documents, screenshots, training information and more. Attach evidence to your system package, a POAM entry, a checklist vulnerability entry or even a compliance statement.
Keep track of all evidence and download as required. All in one spot. And all related to your specific system package.
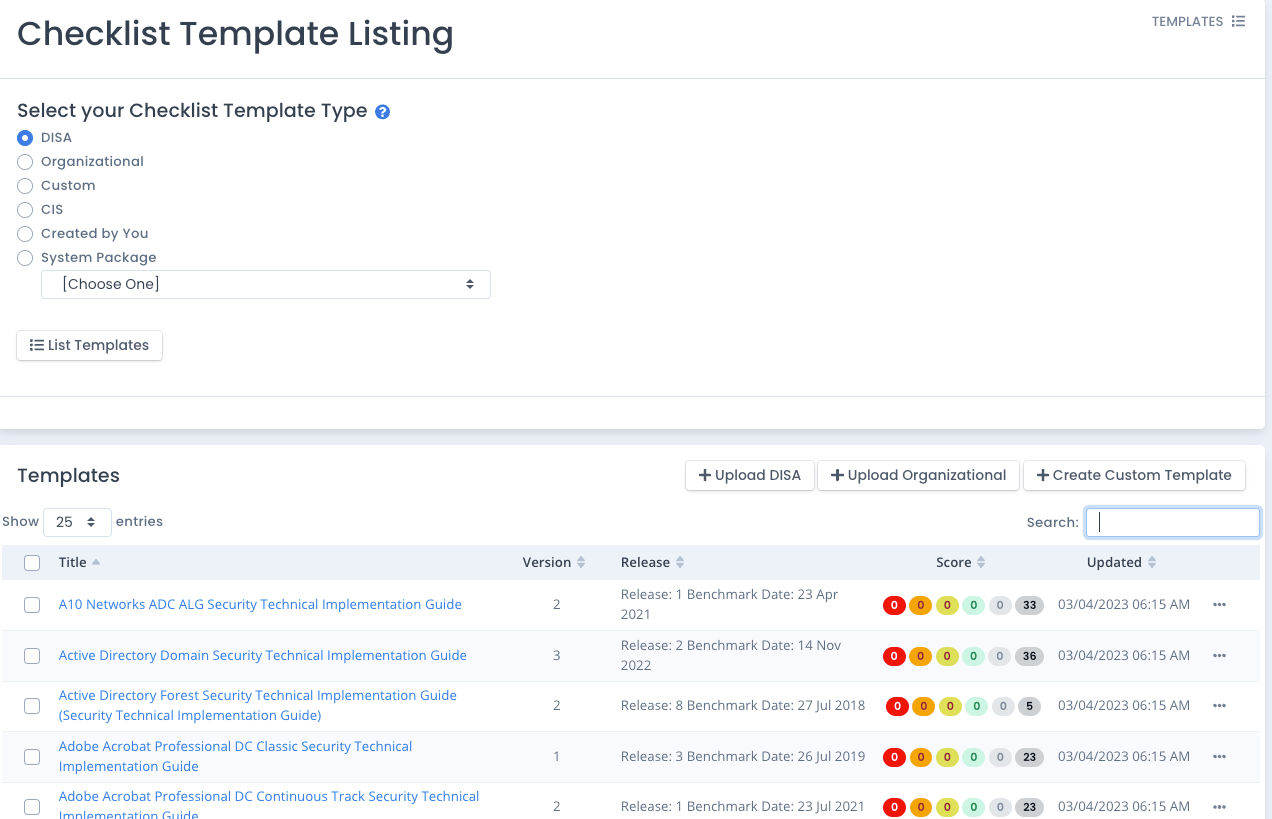
Use the DISA Checklists as-is for Templates to start your Checklists, create CIS checklists from .audit files automatically, or create your own Organization wide or System Package based Template with boilerplate entries on manual vulnerability checks.
Lock vulnerabilities so standard answers are already included.
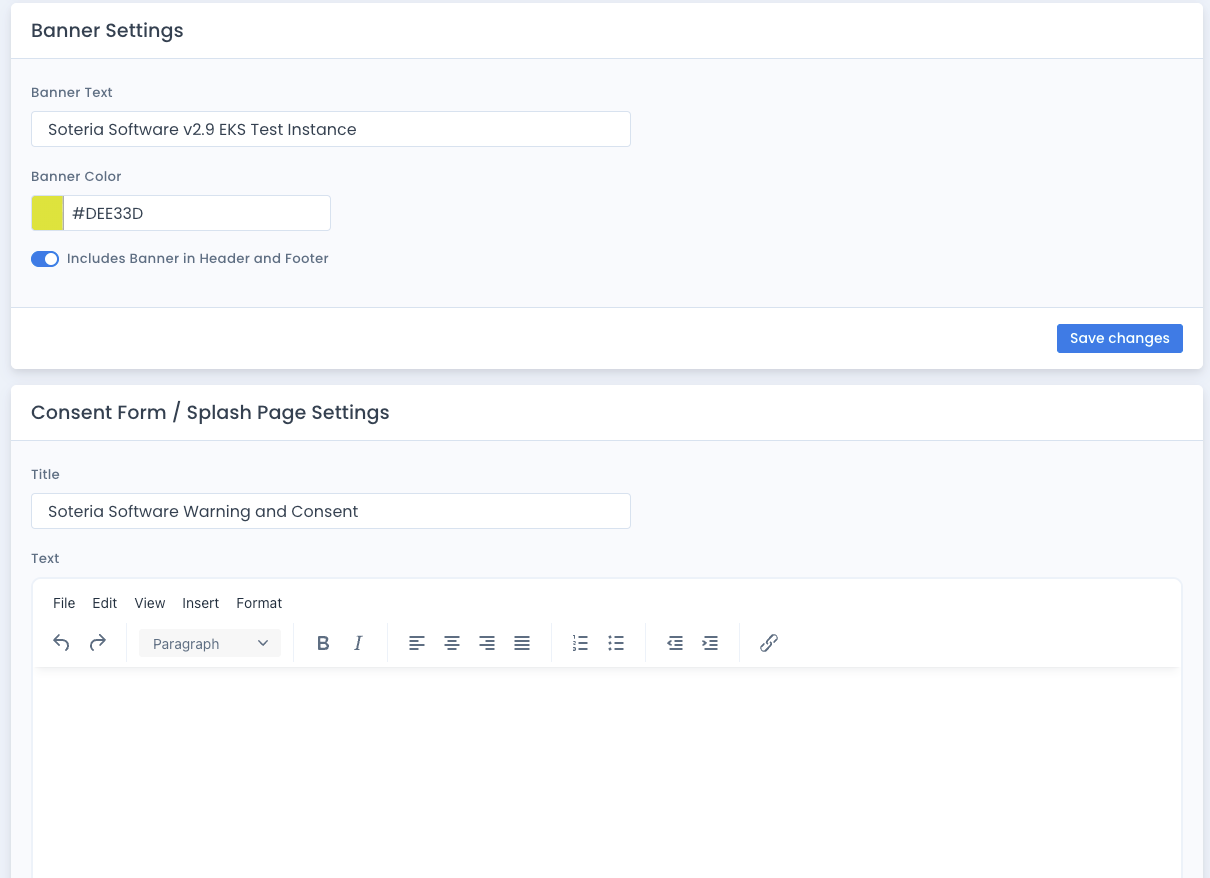
User Theme settings, Robust Audit Filtering, Banner Settings and Consent/Splash page settings allow more control over the user interface.
Specify specific audits to concentrate on based on components, user, timeframe, and more as well.